National Cyber Strategy and the DFARS Mandate
Published:
Dec. 9th, 2018
Recently, the United States Government has indicated that it will step up its efforts to address cyber threats both domestically and internationally. Both the White House and the Department of Defense have released updates of their cyber strategies that detail the fundamental pillars of an effective cyber defense. In this environment, DFARS compliance is now more important than ever for contractors.
While many of these strategies focus on how the United States will operate in the international arena against hostile state actors, there is also a notable focus on defending domestic networks from cyber threats that could compromise them. Each one of the plans includes the protection of the homeland as a pillar.

Presidential National Cyber Strategy
In the White House plan, there are several elements to the protection of our domestic system. The first element is the one that relates closest to NIST 800-171. This element of the pillar calls for securing federal networks and information. The report recognizes the criticality of protecting information that is housed on contractor information systems. The White House Report foreshadows that there will be a unified standard across all of the federal government that will be used in all acquisitions that measure contractors’ information systems.
The White House is particularly concerned about information that belongs to the DOD. The report cites the end result of NIST 800-171 when it says the federal government will be able to assess its data’s security by reviewing the contractor information system. This demonstrates the federal intent to make this an area of focus going forward.
Department of Defense National Cyber Strategy
Similarly, in the DOD report, there is also a heightened focus placed on securing DOD information that is housed on non-DOD systems. The DOD seeks to secure its own networks against malicious cyber attacks. Given the new requirements that contractors face, contractors should take the DOD’s cyber priorities seriously when it says it is seeking to protect its own information no matter where it is housed. The DOD has its own investigative arm, the Defense Contract Audit Agency, that can unleash to perform audits on contractors’ information systems. Thus, you can rest assure that the DOD actually will make this a firm priority in the future.
Contractors will need to ensure that they maintain compliance with the new NIST standard on from now on. If they fail to maintain their DFARS compliance, contractors can lose not only the contracts they have with the United States Government, but they can also be suspended or debarred as government contractors. This is not a position in which anyone who wants to do business with the federal government would want to find themselves.
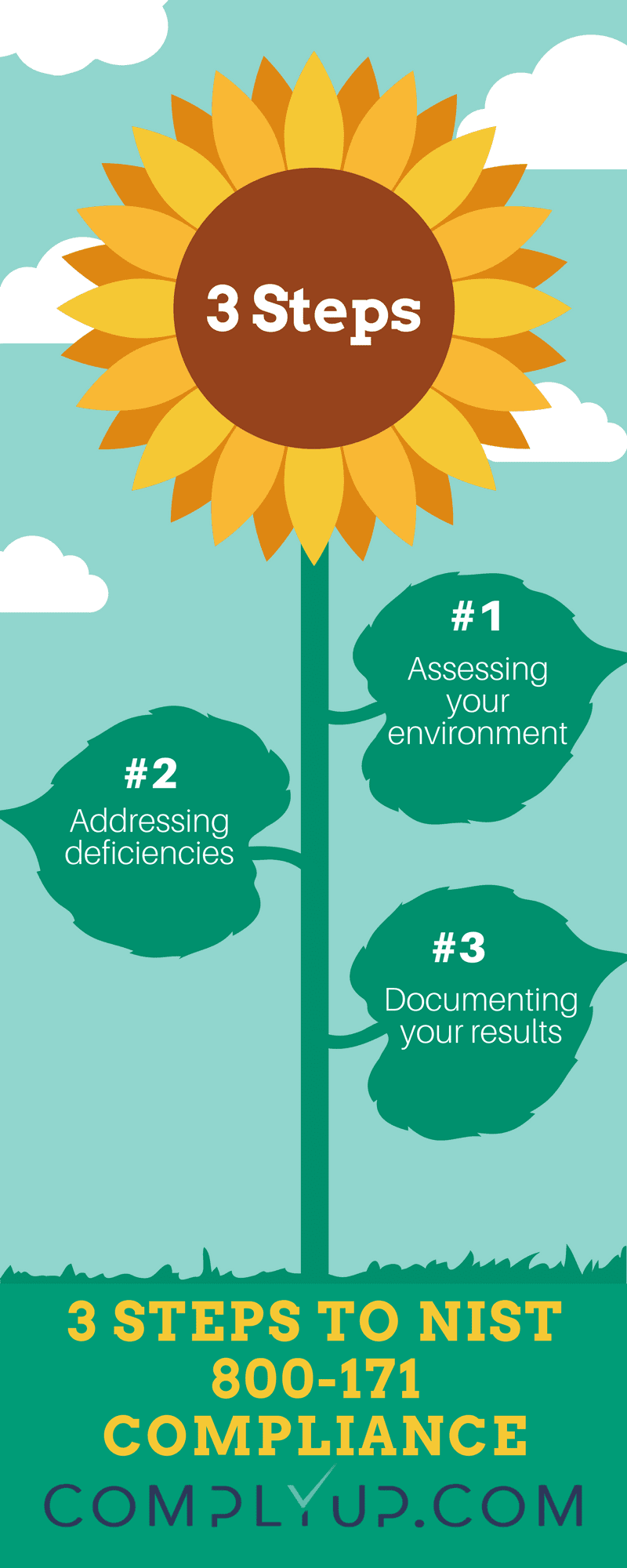
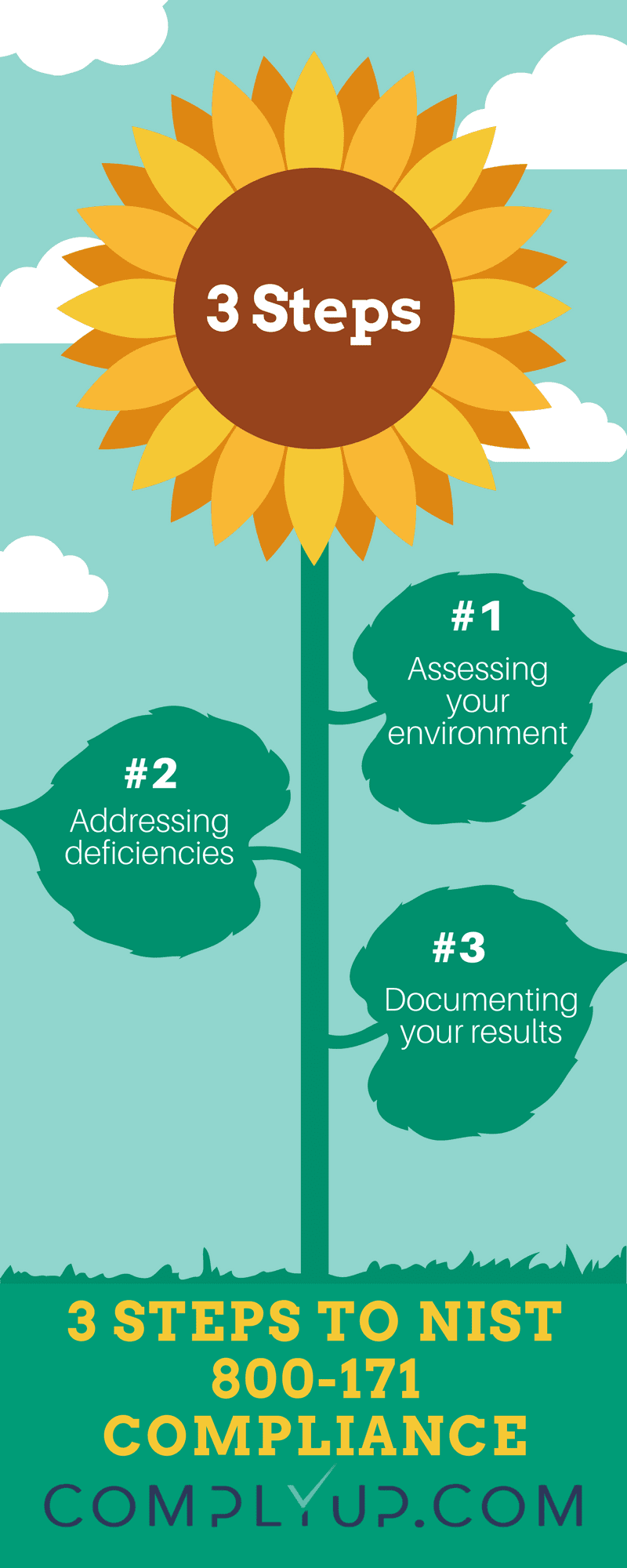
In order to comply with the NIST standards that are aimed at protecting controlled unclassified information, there are a few different compliance options a contractor can use. One of the most cost-effective options involves a NIST 800-171 template. This template will provide your business with the outline of a compliance solution so your business will not be on its own in this vital compliance area. At the same time, this option will be considerably cheaper than hiring a consultant to assist you with compliance.